MLSecOps and DevSecOps Guide Enterprise AI Rollouts
To get AI into enterprise with greater safety and security, firms turning to MLSecOps and DevSecOps to manage vulnerabilities, and get AI developers and IT security pros on the same page
By John P. Desmond, Editor, AI Trends
As AI continues to roll out into the mainstream, substantial risk is associated with its use in the enterprise. IT leaders on the front lines of technology adoption need to be able to trust that the outputs of the AI system are being delivered safely and securely.
This is bringing attention to MLSecOps and DevSecOps as ways to address the security concerns around AI in the enterprise.
“AI is here to stay — and it represents an enormous opportunity. Yet, it’s up to business and technology leaders to ensure that the technology remains safe and secure, and vulnerabilities are managed,” stated Diana Kelley, chief information security officer for Protect AI, offering tools to reduce risk in MLOps pipelines, in a recent account from SC Media.
Company cofounder Badar Ahmed stated in a comment on the website of Protect AI, which was founded in 2022 in Seattle, “We saw a gap between an enterprise’s AI and cybersecurity organizations. Protect AI will be the catalyst to collapse the silos between those teams to help them build safer, more security AI systems to dramatically reduce enterprise risk.”
A survey by international law firm Baker McKenzie cited by Kelley found that while 76 percent of companies deploying AI have policies in place to manage risk, only 24 percent of executives believe the policies are “somewhat effective.”
Kelley cited four core areas of AI risk:
Technical;
Operational;
Regulatory; and
Reputational
Under technical risk, open source models downloaded from repositories can execute code and are often run with high privilege. “We’d expect a company to scan a PDF in email before opening it, but few companies do any scanning of downloaded models before use, leaving them vulnerable to attacks,” Kelley stated.
Governments are stepping up their oversight of AI, with the European Union advancing its AI Act, Canada releasing an AI and Data Act and President Joe Biden issuing an executive order on AI. “Organizations must evaluate how AI and ML fit into regulatory structures and take appropriate steps to mitigate risk,” Kelley stated
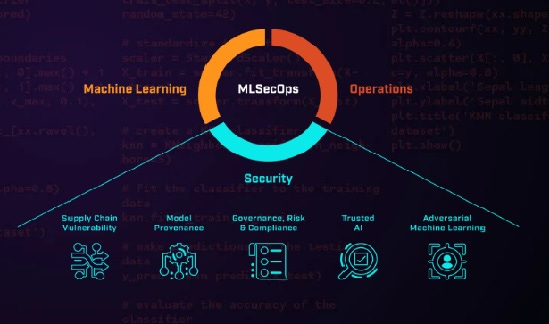
.MLSecOps refers to the integration of security practices into the ML development and deployment cycle, Protect AI states on its website. These practices include: ensuring the security and privacy of data used to train and test models, and protecting deployed models from malicious attacks by using security coding practices, conducting threat modeling and performing security audits. DevSecOps emphasizes collaboration between development, security and operations teams to build security into the software development life cycle through practices such as automated testing.
“MLSecOps focuses on securing machine learning models and processes, while DevSecOps focuses on securing software development and delivery processes,” Kelley stated.
In testimony at a US Congressional hearing on AI security held in December, Protect AI CEO Ian Swanson stated, “Most AI applications and ML systems are highly dispersed and are typically reliant on very common open-source assets … This situation sets the stage for a major security vulnerability … the impact of such a breach on AI systems in the government could be enormous and difficult to quantify, fix and investigate.”
AI Needs to Be On the Defense Team Against Attackers Using AI
In a blog post on the site of Palo Alto Networks, Anand Oswal, VP and GM of network security for the company, stated, “Cybersecurity is the only industry with active adversaries. These adversaries are using the power of AI and ML, and attacks are getting more and more sophisticated.” Palo Alto Networks is a multinational cybersecurity company headquartered in Santa Clara.
Enterprises need to fight fire with fire when it comes to attackers employing AI. “You can only have good cybersecurity through AI and ML. It’s almost impossible to do it manually,” Oswal stated.
An early DevSecOps experience at Comcast demonstrates the effectiveness of the approach. Larry Maccherone got involved in a government-funded research initiative at Carnegie Mellon University’s Software Engineering Institute as part of his software engineering doctorate program. He became a devotee of DevSecOps, and through a friend, Noopur Davis, the Global CISO at Comcast, landed a job at the cable company to help lead a transformation in this area, according to an account from TechTarget.
"The whole idea was to empower software engineering teams to take ownership of security -- build it in, don't bolt it on," stated Maccherone, who has since moved on to be the DevSecOps transformation lead at Contrast Security.
With a staff of 16, Maccherone launched a Dev SecOps pilot program. Of the telecom firm’s 600 application development teams, he identified 10 candidates.
"By my definition, DevSecOps essentially means that empowered engineering teams take ownership of their products all the way to production," Maccherone stated. "It's really the same definition I have for DevOps. To me, DevSecOps is just DevOps done right."
For the DevSecOps pilot, Maccherone's team procured and customized a suite of automated security testing tools that Comcast developers could easily integrate with their own continuous integration/continuous delivery (CI/CD) pipelines. This eliminated the need to pass software to the application security team, which could take weeks to review it.
"We basically said, 'Here's tooling that works the way developers work and thinks the way developers think, that plugs into your pipeline and provides the feedback directly to you,'" Maccherone stated.
Eventually, about 100 of Comcast's software development teams were practicing DevSecOps. The results were compelling, with those groups seeing 85 percent fewer security incidents in production than their legacy counterparts, according to the account.
Within five years, about half of Comcast's 600 or so development teams had joined the DevSecOps transformation program. The company decided to shut down its traditional application security program, so that instead of a siloed team of 400 security specialists, the company would have 100 DevSecOps pros.
"That essentially solved Comcast's cybersecurity hiring problem," Maccherone stated. "We were able to do 85 percent better risk reduction with a quarter of the staff."
MLSecOps Can Defend Against Model and Data Poisoning
For MLSecOps, experts at Harrison Clarke, a staffing and recruiting firm focused on cybersecurity and AI, recommend companies need to integrate cybersecurity practices with ML operations. “Having a dedicated team for securing machine learning models is no longer a luxury but a necessity,” stated an account on the Harrison Clarke website. This is to protect against adversarial attacks, model poisoning and data poisoning.
Harrison Clarke was founded in 2017 by Firas Sozanl, who serves as CEO.
MLSecOps practices advocated by Harrison Clarke include regular adversarial testing, to discover and patch vulnerabilities before they are exploited. “By subjecting models to a variety of adversarial scenarios, teams can iteratively improve their robustness,” the account states.The essential skills to include on an MLSecOps team, the firm recommends:
Machine learning expertise;
Cybersecurity knowledge;
Data governance specialists; and
DevOps and IT skills
“Collaboration is the cornerstone of a successful MLSecOps team,” the company advises.
The city of Las Vegas committed to the use of AI for cybersecurity some 10 years ago, when it started working with Darktrace, the UK-based software company founded in 2013 by mathematicians and cyber defense experts. The city was looking to gain an edge on potential attackers, especially by spotting subtle signs of emerging cyber incidents while still in their early stages.
“Every cyber-attack is different,” stated Michael Sherwood, chief innovation and technology officer for Las Vegas, in a case study on the Darktrace website, adding. “And there will never be enough human staff to defend against the variety of threats in today’s landscape.”
Seeing good results from the initial deployment, Las Vegas has since expanded Darktrace’s coverage to its cloud infrastructure, email systems and industrial networks.
Read the source articles and information from SC Media, on the website of Protect AI, from TechTarget. on the Harrison Clarke website, and in a case study on the Darktrace website.






